It’s never a good time to let your guard down.
In the whirlwind of running a small business, IT security can easily slip through the cracks. Consider us your reliable lighthouse, guiding you to the safety of robust cybersecurity.
Complete our five-minute assessment and join other Burlington Chamber members in strengthening your IT defenses.
%
of reported cyber incidents in Canada impact SMB.
With cyber threats escalating, no business, big or small, is immune to the risks.
Small businesses are not just operationally unique but also uniquely vulnerable. The rise in cyber attacks highlights the critical need for robust cybersecurity measures. It’s not just about protecting data; it’s about safeguarding your business’s future, reputation, and the trust of your customers. Today, more than ever, effective IT security is a cornerstone of business resilience and success.
Participating in our five-minute assessment will give you invaluable insights into your cybersecurity stance, aligning your business with the proactive approach of fellow Burlington Chamber members. This isn’t just an assessment; it’s a step towards empowering your business against the ever-evolving cyber threats.
Your Path to Enhanced Cybersecurity
Submit your Assessment
Begin by sharing insights about your current IT infrastructure through our comprehensive assessment.
Analysis of Your Results
Our team of experts will meticulously analyze your responses to gauge your cybersecurity stance.
Customized Report
Within 3 business days, receive a personalized report with your cybersecurity score and recommendations to boost cybersecurity readiness.
Expert Guidance
If you need guidance on the next steps, we’re here to help cover any gaps and strategize for a robust cybersecurity framework.
Begin assessment.
Please answer these questions to the best of your knowledge. Your honest responses will lead to recommendations for better cybersecurity for your business in 2024.
While you wait…
The IT Partner Every Business Needs at the Table
Strategic IT advice before decisions are made prevents surprises and costs. Many business decisions that seem unrelated to technology actually have important IT implications. Vendor tools, office expansions, grant applications, and new initiatives often affect...
The Hidden Risk Of Relying On A Single Internal “Hero”
From Single Point of Failure to Seamless Resilience: Why Your Best Employee Might Be Your Biggest Risk. Every SMB has them. The person everyone calls when something goes wrong. Is the printer jammed again? Call Priya in accounting. Is the Wi-Fi down? Call Casey in...
Windows Server 2016 End of Life: Upgrade or Replace? How SMBs Should Decide
Windows Server 2016 is approaching end of support. When that happens, the risk and accountability around that server change. For many SMBs, the default reaction is understandable: “We need to upgrade.” “What’s the next version?” Reasonable. But this is where most IT...
SMB Leaders Step Forward: Make Technology a Lever, Not a Liability
Smart SMBs know IT isn’t just about keeping the lights on – it’s about leading with intent. Discover how to guide technology decisions strategically and turn IT into a true driver of growth, efficiency, and confidence for your business.
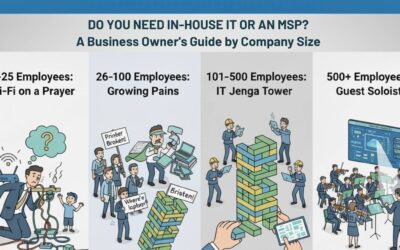
Do You Need In-House IT or an MSP?
Still asking “who’s fixing the Wi-Fi?” every Monday morning? You’re not alone. This guide breaks down when to stick with DIY IT, hire in-house, or call in an MSP—based on your company’s size and growth.