Challenge #12
Strengthen Administrative Security with MFA
Elevate the security of your administrative accounts in Microsoft 365 by implementing Multi-Factor Authentication (MFA), a crucial step in defending your organization’s core operations.

Why?
Administrative accounts in any organization are akin to holding the keys to the castle. They possess elevated access and control, making them prime targets for cyber attacks. Simply having a strong password is no longer sufficient for these high-stakes accounts. That’s where Multi-Factor Authentication (MFA) comes into play.
Implementing MFA for administrative roles is more than an added security layer; it’s a fundamental necessity. MFA requires a secondary form of verification, such as a code from a mobile app or a biometric scan, making it exponentially harder for unauthorized individuals to gain access. This means that even if a password is compromised, the chances of a security breach are significantly minimized. For small and medium-sized businesses (SMBs), where every resource counts, MFA offers an efficient, cost-effective way to safeguard your most sensitive and critical access points.
How?
Microsoft has largely enabled multifactor authentication policies to protect administrative accounts in Microsoft 365. Let’s ensure our settings protect our critical administrative accounts.
Step 1: Go to the Microsoft Entra Admin Center
On your computer, launch a new browser window (Edge, Chrome), and type in https://entra.microsoft.com/ and press enter.
Note: You will require Microsoft 365 administrative credentials – be sure to have the username and password ready.
Step 2: Access Identity Protection
Within the Microsoft Entra Admin Center:
- Look for and select Identity on the left-hand menu
- Under Identity select Identity Protection
- Now select Conditional Access
Step 3: Validate or Create a Conditional Access Policy
- Within the Conditional Access window, select Policies
- Now select the Require MFA for admins policy
- If this policy does not exist, select New policy and follow along to match the required settings
Step 4: Validate or Define our Conditional Access Policy settings for Users
- Within the Require MFA for admins policy window, scroll down and select the link under Assignments / Users
- In the new blade that opens, under Include we want to Select users and groups, and Directory Roles as the only checked option.
- Now, select the drop down box, and check the mark beside each built-in directory roles to include in the policy:
- Application Administrator
- Authentication Administrator
- Authentication Policy Administrator
- Billing Administrator
- Cloud Application Administrator
- Conditional Access Administrator
- Exchange Administrator
- Global Administrator
- Groups Administrator
- Helpdesk Administrator
- License Administrator
- Office Apps Administrator
- Password Administrator
- Power Platform Administrator
- Privileged Authentication Administrator
- Privileged Role Administrator
- Security Administrator
- Service Support Administrator
- SharePoint Administrator
- Teams Administrator
- User Administrator
Step 5: Validate or Define our Conditional Access Policy settings for Target Resources
- Still within the Require MFA for admins policy window, scroll down and select the link under Target Resources
- In the new blade that opens, under Include we want to select All cloud apps
Step 6: Validate or Define our Conditional Access Policy settings for Target Resources
- Still within the Require MFA for admins policy window, scroll down and select the link under Target Resources
- In the new blade that opens, under Include we want to select All cloud apps
Step 7: Enable Policy
- Still within the Require MFA for admins policy window, scroll down and select enable policy to be On
- Now, on next login, administrative accounts will be prompted to enroll with Microsoft Authenticator.
While you’re here…
The True Cost of Cheap IT: When Saving Now Costs You Later
Choosing the lowest IT bidder is a false economy. Learn why those initial savings vanish instantly once you are hit with constant downtime, security breaches, and frustrated staff. Real IT leadership isn’t about saving a few dollars a month; it’s about strategic investment that prevents catastrophic costs down the line. Find out what you truly deserve from an MSP.
SMB Leaders Step Forward: Make Technology a Lever, Not a Liability
Smart SMBs know IT isn’t just about keeping the lights on – it’s about leading with intent. Discover how to guide technology decisions strategically and turn IT into a true driver of growth, efficiency, and confidence for your business.
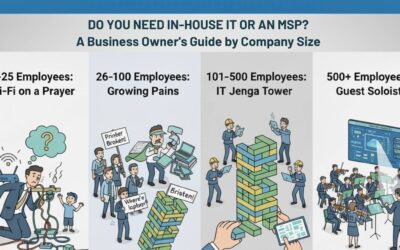
Do You Need In-House IT or an MSP?
Still asking “who’s fixing the Wi-Fi?” every Monday morning? You’re not alone. This guide breaks down when to stick with DIY IT, hire in-house, or call in an MSP—based on your company’s size and growth.