Challenge #9
Secure Sharing with Automatic Guest Expirations
Implement automatic expiration for guest access in SharePoint and OneDrive. Ensure your external collaborations are both productive and secure.

Why?
Collaborating with external partners is vital, yet it brings its own set of security challenges. Granting guest access to SharePoint and OneDrive via file shares, Microsoft Teams invites or related is a common practice, but without proper controls, it can leave our data vulnerable. By setting automatic expiration for guest access, we add a layer of security that adapts to the dynamic nature of collaboration.
This approach ensures that external partners have access only for as long as they need it, typically recommended for no more than 30 days. After the set period, access expires automatically, reducing the risk of outdated permissions lingering and potentially becoming security loopholes. It’s about creating a secure environment where access is granted judiciously and monitored continuously, aligning with the best practices for data protection.
How?
Configuring automatic expiration for guest access in SharePoint and OneDrive is a straightforward but critical step in enhancing your collaborative security. Here’s how to get that gap closed up.
Step 1: Go to the Microsoft Sharepoint Admin Center
On your computer, launch a new browser window (Edge, Chrome), and type in https://admin.microsoft.com/sharepoint and press enter.
Note: You will require Microsoft 365 administrative credentials – be sure to have the username and password ready.
Step 2: Adjust Sharing Policies
Within the Microsoft Sharepoint Admin Center:
- Look for and select Policies
- Under Policies, select Sharing
Step 3: Configure External Sharing Settings
- Within the Sharing window, find and click More external sharing settings (it’s an expandable menu).
- Under More external sharing settings, find and enable the setting for Guest access to a site or OneDrive will expire automatically after this many days
- Once enabled, you can then define the days in which you are comfortable with, ranging from 30 to 730 days.
- We recommend 30 days
PS. For bonus points, there are several other settings on this page that can improve security and your Secure Score, such as default permissions for sharing links (view vs. edit), defaults for who can use the links when you share files, and several others. Explore.
Step 4: Confirm and Save Settings
- Once you are satisfied with your changes, click Save
While you’re here…
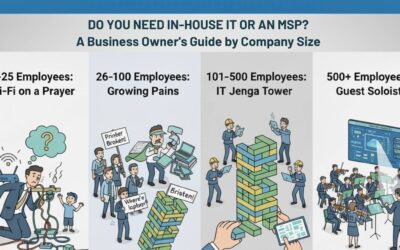
Do You Need In-House IT or an MSP?
Still asking “who’s fixing the Wi-Fi?” every Monday morning? You’re not alone. This guide breaks down when to stick with DIY IT, hire in-house, or call in an MSP—based on your company’s size and growth.
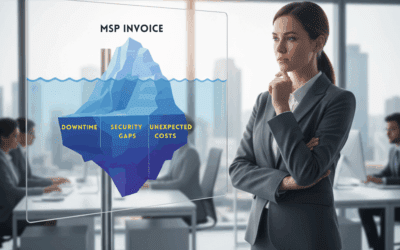
The 3 Hidden Costs of a “Good Enough” MSP
Most leaders rate their IT provider a 7 out of 10—safe, but not stellar. The problem? A “good enough” MSP hides costs that quietly erode your business: downtime employees don’t bother reporting, compliance gaps attackers exploit, and unpredictable invoices that wreck your budget. Here’s what those hidden costs look like—and how a proactive MSP can flip IT from a liability into a growth driver.
Technology Choices Shouldn’t Be a Gamble: How SMBs Can Make Smarter, Safer Decisions
Navigating the technology marketplace can feel like a gamble for small and mid-sized businesses. Without a deep IT background, leaders often make hurried, ill-informed decisions that lead to hidden costs, security risks, or the wrong solution entirely. This post shows you how to avoid common pitfalls, ask better questions, and make technology choices that truly fit your business goals.