Challenge #3
Secure Data by Restricting User Consent
Enhance your data security by managing user consent for applications in Microsoft 365. Ensure every app accessing your company’s data receives your explicit approval.

Why?
Every application your team uses could be a gateway to sensitive company data. But what if users, unknowingly or accidentally, give these applications access to your information? That’s where the power of restricting user consent comes into play. This setting in Microsoft 365 ensures that any application seeking access to your data doesn’t get a free pass—it must be approved by you, the administrator, or whoever is responsible for IT (e.g., Third Octet).
Think of your company data as a treasure that needs guarding. Without proper oversight, it’s like leaving the treasure chest unlocked. By managing user consent, you’re effectively putting a robust lock on this chest. This way, only applications that have your explicit permission can access your precious data, keeping out those that might misuse it. Remember, it’s not about limiting your team’s tools; it’s about making sure each tool is safe and right for your business.
How?
Adjusting your Microsoft 365 settings to restrict user consent is straightforward. Here’s how to ensure that applications access your company data only with your approval:
Step 1: Go to the Entra Admin Center
On your computer, launch a new browser window (Edge, Chrome), and type in https://entra.microsoft.com/ and press enter.
Note: You will require Microsoft 365 administrative credentials – be sure to have the username and password ready.
Step 2: Navigate to Application Settings
Within the Microsoft Entra Admin Center:
- Look for and select Identity along the left-hand side menu
- Under Identity, look for and select Applications
- Under Applications, select Enterprise applications
Step 3: Modify Consent and Permissions
- Within the Enterprise applications window, under Security, find and select Consent and permissions
Step 4: Set Restriction on User Consent
- Within Consent and user permissions, find the section for User consent for applications
- There are three available options:
-
Do not allow user consent: An administrator will be required for all apps.
-
Allow user consent for apps from verified publishers, for selected permissions: All users can consent for permissions classified as “low impact”, for apps from verified publishers or apps registered in this organization.
-
Allow user consent for apps: All users can consent for any app to access the organization’s data.
-
- While Microsoft may recommend Allow user consent for apps from verified publishers, we prefer the more restrictive option Do not allow user consent.
- Both options are inherently more secure than the last option, Allow user consent for apps
Step 5: Save Your Settings
- Once you are satisfied, click Save by selecting the Save icon on the top of the User consent settings window.
While you’re here…
How We Work at Third Octet: A Clear, Predictable IT Partnership
A clear, guided path from first conversation to long-term IT confidence A proven approach trusted by nearly 100 Canadian SMBs to simplify, secure, and modernize IT. Without surprises. This page is for growing SMBs (typically 25–150 employees) who have outgrown “basic”...
Protecting Cash Flow and Continuity: Why SMBs Need Cyber Insurance Now
A fundamental question we hear more than ever On a recent call with one of our long-time clients, their finance lead paused and asked a simple, yet loaded question: "We're a small business. Is cyber insurance really necessary?"It's a fair question. A question that...
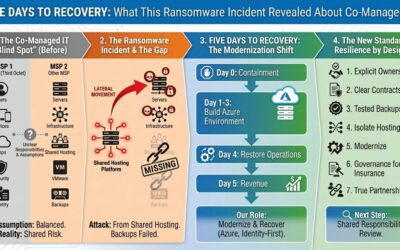
Five Days to Recovery: What This Ransomware Incident Revealed About Co-Managed IT
A story of shared hosting, broken assumptions, and the 'blind spot' in co-managed accountability Ransomware hit shared infrastructure managed by another provider.Backups failed.The business went offline.Operations were restored in five business days. Here’s what...