Most Canadian SMBs have the right technology in place. What’s missing is the plan behind it.
For many SMBs, two things can be true at the same time: your security tools are strong, and your business is still less prepared than you think.
Here’s what that looks like in practice. You’ve got antivirus, backups, and MFA on most accounts. Your IT provider sends a monthly report, and the numbers look reasonable. You’ve done the responsible thing, and you’re not losing sleep over it.
Then a phishing email lands. An employee clicks something. An account gets compromised.
And suddenly, the conversation in your office sounds like this: “Who do we call? What do we do first? Are we supposed to notify anyone? How do we know what they actually got access to?”
Silence. Not because you have bad technology, but because nobody ever wrote down the answers.
Good tools help. But they don’t tell your team what to do next.
Let’s be direct about something the managed IT industry doesn’t say often enough: the security tools most Canadian SMBs are running today are actually pretty solid. Microsoft 365 Business Premium alone includes identity controls, endpoint management, threat detection, and backup. Configured properly, it covers a lot of ground.
But here’s what no security dashboard tells you. Tools define what your technology can do. What protects you in a real incident is whether your team knows what to do next, and whether anyone has written it down.
The rules. The plan. The “who does what” when something goes sideways.
That’s the layer most businesses skip. Not because they don’t care, but because nobody ever asked them to think about it.
Without it, you can have a strong setup and still be unprepared.
The 30-second version: Your security tools are probably fine. What most SMBs are missing isn’t technology — it’s a written plan for when something goes wrong. Who calls who. What gets shut down. What gets communicated. That’s the Governance Gap, and it’s fixable without a big project.
Five quick questions. Answer them honestly.
Don’t look anything up. Just answer these right now:
1. Do you have a written acceptable use policy that clearly outlines what employees can and can’t do with company technology and data?
2. Do you have a written incident response plan that specifies who does what and in what order if something serious happens tonight?
3. Do your employees know which AI tools they’re allowed to use for work, and which ones could put client data at risk?
4.Do you have a clear, enforced policy for remote work and personal devices?
5. If something went wrong today, could you tell your cyber insurer, your clients, or your board exactly what happened and when?
Most businesses we talk to can answer one or two. Some can’t answer any.
That’s not a technology failure. The technology is usually fine. It’s a planning gap, and that gap is where real incidents turn into real disruptions.
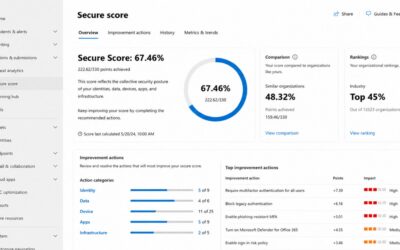
What a security score won’t tell you
Security scores are useful. We look at them too. But a score tells you how well your tools are configured. That’s it.
It doesn’t tell you whether your team knows what to do with a suspicious email, whether employees are using AI tools in ways you never approved, or how your organization would actually function in the first hour of a real incident.
We worked with an organization recently that had strong Microsoft 365 controls, solid MFA enforcement, and a reasonable security score. What they didn’t have was documented clarity on who owned incident decisions internally.
When an issue surfaced, the delay wasn’t technical. It was people waiting for someone else to make the call.
What should have been a contained, 30-minute response stretched into hours of confusion across leadership, IT, and operations. That’s a fixable problem, but only if you address it before something forces you to.
“My current IT provider should be handling this.”
They should. But most traditional IT assessments focus on your tools: what’s installed, what’s configured, and what the dashboard shows.
The policy and planning layer is a conversation entirely its own, and most providers aren’t having it. Not because they’re negligent, but because the industry has historically drawn the line at technology. Technical health checks are standard. Organizational readiness reviews are not.
That means it often falls to the business itself to ask the question, and most businesses don’t know to ask it until something goes wrong.
This isn’t about creating a binder no one reads
The fix here isn’t complicated and isn’t a massive project. It’s about making sure your business has a few clear written rules and a simple plan before something forces the issue.
For most SMBs, that starts with five basic areas: acceptable use, data handling, AI and shadow IT, incident response, and remote work. If AI use is part of the challenge, it can help to define how to manage shadow IT without slowing your team down.
The goal isn’t documentation for its own sake. It’s making sure your team knows what to do, your leadership knows who’s in charge, and your business can respond clearly when it counts.
Less confusion in a crisis. Less downtime. Less risk to client relationships and your reputation. Less dependence on whoever happens to be in the building that day.
Not sure where you stand?
That’s what the Governance Gap Report is for. It’s a simple leadership readiness review. We’re not scanning devices or running vulnerability tests. We’re looking at whether your business has clear, usable answers in the areas that matter most when something goes wrong.
Most IT assessments focus on your tools. This one focuses on whether your leadership team actually has a plan.
If you want a clear picture of where your biggest gaps are, book a 60-minute Governance Gap review. It’s a focused conversation, not a technical audit. Book your review.



0 Comments